It was 2:00 a.m. at a global fintech company in Singapore. The system was handling over two million concurrent transactions per second — every trade, every payment, every validation moving through millions of threads that never seemed to rest.
Suddenly, a spike in latency threatened to halt an entire financial region. The engineers, instead of panicking, deployed their new Java 2026 runtime — built on Virtual Threads, Generational ZGC, and Scoped Values.
In less than a minute, the system stabilized.
No thread contention. No garbage collection freeze. No loss of data.
For the first time in years, the engineers watched their dashboard go from red to green — and the code finally slept.
That moment didn’t just save a night of transactions. It marked a turning point for Java itself — a language that, after nearly three decades, has once again reinvented how we build, scale, and secure the digital world.
Java 2026 isn’t an update. It’s a transformation.
It fuses the reliability of the JVM with the power of native systems — introducing Virtual Threads, Pattern Matching, Project Panama, Vector API, Generational ZGC, and Post-Quantum Security.
The result? A platform that runs faster, safer, and more intelligently than ever before — ready for the next era of cloud, AI, and data-driven innovation.
Overall Summary
| Category | Feature | Technical Focus | Key Advantage | Practical Impact |
|---|---|---|---|---|
| Concurrency & Parallelism | Project Loom (Virtual Threads, Structured Concurrency) | Lightweight JVM-managed threads, structured task scopes | Handles millions of concurrent tasks with low overhead | Ideal for microservices, cloud servers, and real-time APIs |
| Language Enhancements | Pattern Matching & Record Patterns | Type-safe data deconstruction and concise condition handling | Reduces boilerplate and improves readability | Simplifies complex data flow and switch logic |
| Text Processing | String Templates | Inline variable interpolation and validation | Eliminates concatenation errors; secure by design | Cleaner code for logging, SQL, and JSON |
| Native Integration | Project Panama (Foreign Function & Memory API) | Safe interop with C libraries and off-heap memory | JNI-level performance without unsafe code | High-performance computing, AI, and system integration |
| Performance Computing | Vector API (SIMD Operations) | Hardware-level vectorization for arrays and math operations | Up to 15× faster compute workloads | Machine learning, cryptography, image processing |
| Memory Management | Generational ZGC (Garbage Collection) | Low-latency GC with generational memory regions | Sub-1ms pause times at massive heap sizes | Predictable performance for large-scale systems |
| Security | Post-Quantum Cryptography (KEM API) | Quantum-resistant encryption primitives | Future-proof key security and encapsulation | Defense, finance, and government-grade protection |
| Context Management | Scoped Values | Immutable, scope-based data sharing | Safely replaces ThreadLocal | Cleaner concurrency models, reduced memory leaks |
| Experimental & Preview Features | Stream Gatherers, Flexible Constructors, Class-File API | Enhanced developer control and data collection | Faster prototyping and dynamic bytecode analysis | Framework and toolchain development |
| Ecosystem Performance | JVM & JIT Enhancements | Integration with HotSpot and Graal optimizations | Reduced startup time and improved runtime performance | Higher throughput for modern Java applications |
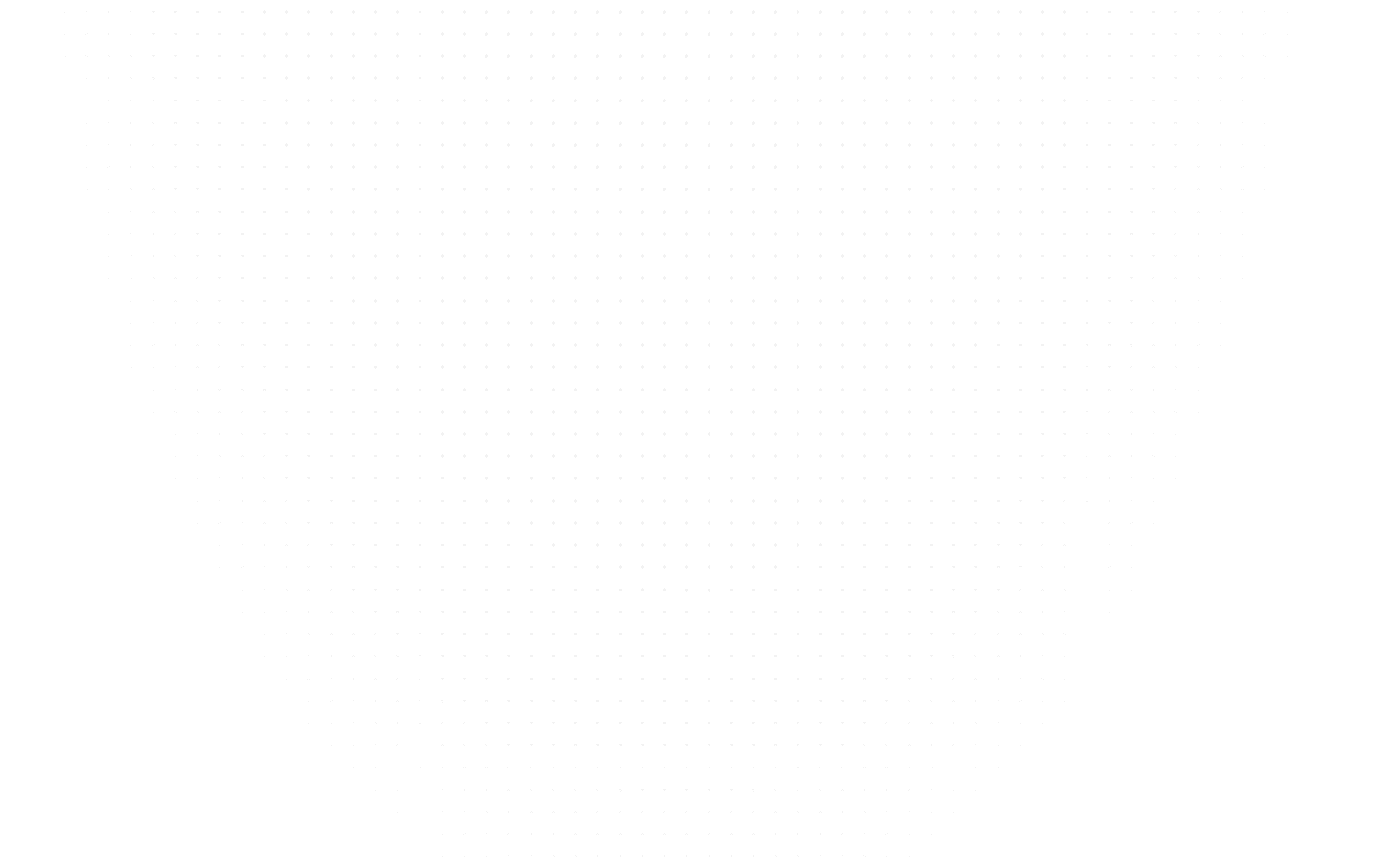
The Evolution of Java
Since Java’s inception in 1995, its central goal has remained “Write Once, Run Anywhere.” Each new release brought innovations that kept pace with changing computing paradigms — from desktop and enterprise systems to mobile and cloud-native ecosystems. The 2025 release introduces technologies like Project Loom, Pattern Matching Enhancements, String Templates, and Project Panama, ensuring Java’s continued dominance in AI, cloud, and distributed computing environments.
Core Objectives of Java 2026
- Simplify Concurrency: Virtual Threads and Structured Concurrency make multi-threaded programming efficient and intuitive.
- Improve Readability: Pattern Matching and Record Patterns reduce boilerplate and enhance clarity.
- Enhance Security: Built-in validation mechanisms and advanced cryptographic APIs strengthen application integrity.
- Enable Native Performance: The Foreign Function & Memory API bridges Java with native code without JNI overhead.
- Modernize Syntax: Features like String Templates introduce expressive, secure text interpolation.
Significance for Developers
Java 2026 focuses on eliminating accidental complexity. Developers can now write code that is:
- Synchronous in style but asynchronous in performance (Virtual Threads).
- Declarative and readable (Pattern Matching).
- Secure by design (Validated String Templates).
- Native-capable (Project Panama).
In essence, Java 2026 empowers developers to build highly scalable, secure, and performance-driven systems using cleaner and safer code.
Project Loom: Virtual Threads and Structured Concurrency
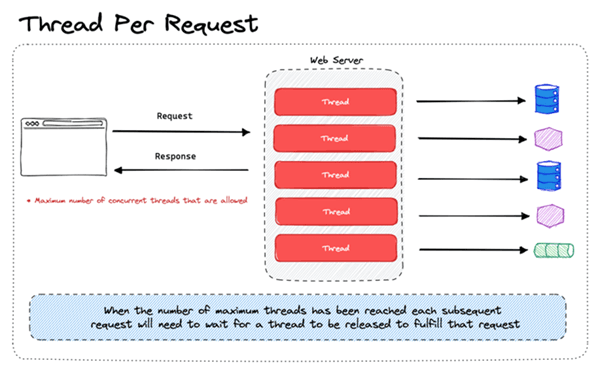
Concurrency in Java has long been both powerful and complex. Traditional threads were expensive system resources; creating thousands could overwhelm the OS. Project Loom, introduced in Java 21 and perfected by 2025, revolutionizes this with Virtual Threads and Structured Concurrency, making it possible to write simple, blocking-style code that still scales to millions of concurrent tasks.
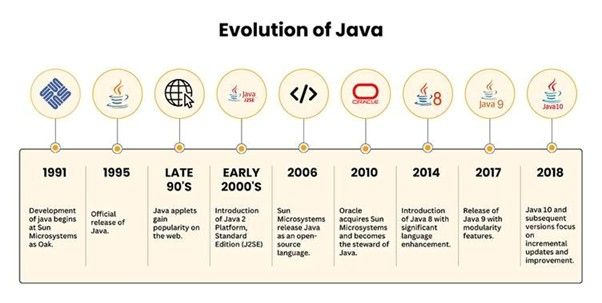
Understanding Virtual Threads
Concept Overview
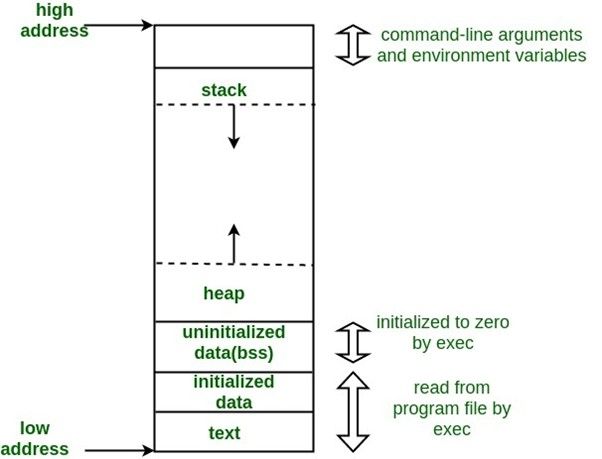
A Virtual Thread is a lightweight thread managed entirely by the Java Virtual Machine (JVM), not the operating system. They behave like regular threads but consume far fewer system resources. Unlike platform threads, which are tied to OS threads, virtual threads are multiplexed onto a smaller pool of carrier threads.
How They Work
When a virtual thread blocks (e.g., waiting for I/O), the JVM unmounts it from its carrier thread, allowing the carrier to run other virtual threads. When the blocking call completes, the JVM remounts the virtual thread.
This model ensures:
- High concurrency with low memory usage.
- Natural, readable code (blocking style).
- No callback hell or complex asynchronous constructs.
Key Advantages
- Scalability: Millions of concurrent tasks possible.
- Simplicity: Code looks like synchronous Java but performs asynchronously.
- Compatibility: Works seamlessly with existing libraries and frameworks.
- Efficiency: Ideal for I/O-heavy workloads such as web servers and data pipelines.
Example: Virtual Thread Basics
public class VirtualThreadExample { public static void main(String[] args) throws InterruptedException { Thread vt = Thread.ofVirtual().start(() -> System.out.println("Running in: " + Thread.currentThread())); vt.join(); } }
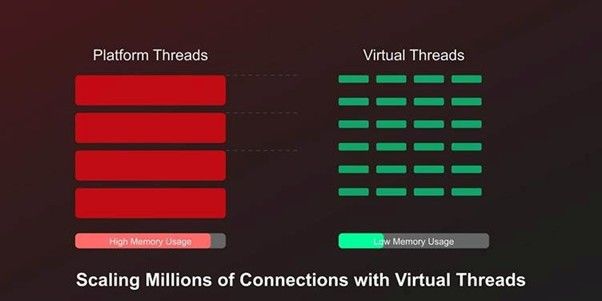
Structured Concurrency
The Problem It Solves
In traditional Java, concurrent tasks were managed individually, often leading to thread leaks, partial failures, and unstructured lifecycles. Structured Concurrency introduces a model where concurrent tasks are grouped, managed, and terminated together, forming a structured task scope.
Core Principles
- Scope-based Lifecycle: Tasks start and finish within a defined scope.
- Error Propagation: If one task fails, others are canceled automatically.
- Simplified Cancellation: No orphaned threads or unhandled exceptions.
- Better Debugging: Stack traces reflect logical structure, not chaos.
Example: Fetching Parallel Tasks
import java.util.concurrent.*; public class StructuredConcurrencyDemo { static String fetchData(String source) throws InterruptedException { Thread.sleep(500); return "Data from " + source; } public static void main(String[] args) throws InterruptedException { try (var scope = new StructuredTaskScope.ShutdownOnFailure()) { Futureapi1 = scope.fork(() -> fetchData("API 1")); Future api2 = scope.fork(() -> fetchData("API 2")); scope.join(); scope.throwIfFailed(); System.out.println(api1.resultNow() + " & " + api2.resultNow()); } } }
- Line-by-Line Explanation
- StructuredTaskScope.ShutdownOnFailure() defines a scope where if any task fails, all are canceled.
- scope.fork() starts each concurrent task.
- scope.join() waits for completion.
- scope.throwIfFailed() propagates the first error.
- resultNow() retrieves completed results.
This structure ensures that concurrent operations either all succeed together or fail together — maintaining logical integrity.
Practical Implementation Examples
Use Case 1: High-Concurrency Web Server
A web server can now handle millions of requests by assigning one virtual thread per connection. Each request remains isolated yet consumes minimal resources.
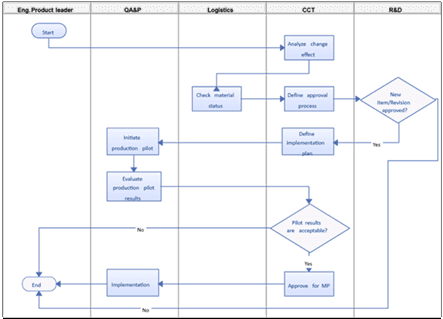
Use Case 2: Financial Systems
Structured Concurrency ensures that multi-step transactions (like debit, credit, and logging) execute atomically. If one operation fails, all associated ones cancel automatically
Use Case 3: Real-Time Data Streams
Virtual Threads handle I/O operations from multiple data sources concurrently, ensuring smooth aggregation and faster responses without resource exhaustion.
Pattern Matching Enhancements
Pattern Matching enhances Java’s type-checking and control flow by allowing developers to match object types directly and decompose data structures succinctly. This feature significantly reduces boilerplate and improves code safety.
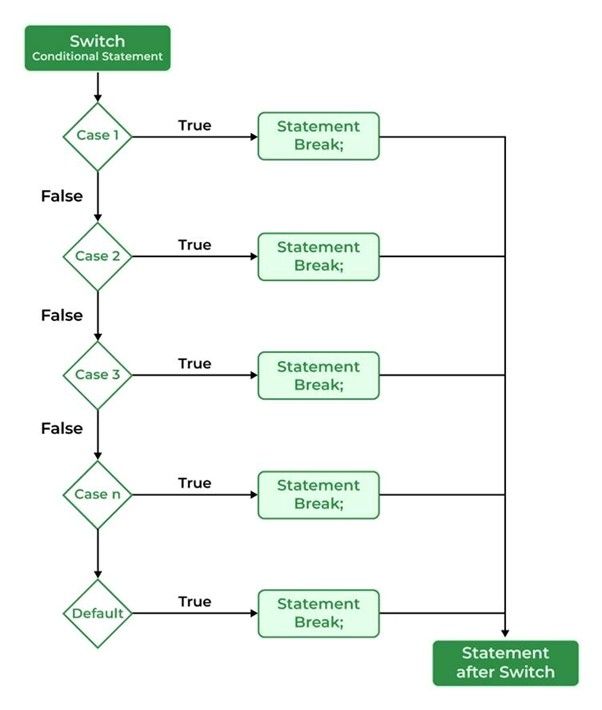
Pattern Matching for Switch
Overview
Traditionally, switch statements could only handle primitive values or enums. Java 2025 extends this to objects and patterns, making switch both type-aware and expressive.
Example: Smart Type Matching
static String describe(Object obj) { return switch (obj) { case Integer i -> "Integer: " + i; case String s -> "String (len=" + s.length() + ")"; case Double d when d > 0 -> "Positive double: " + d; case null -> "Null reference"; default -> "Unknown type"; }; }
- Explanation
- case Integer i performs type check + automatic cast.
- when acts as a guard condition.
- default ensures exhaustiveness. This pattern eliminates instanceof checks and manual casting.
Use Case
Used in data transformation pipelines, message dispatchers, and object inspection utilities where dynamic types are common.
Record Patterns
Definition
Record Patterns allow deconstruction of record objects into individual components directly in expressions or conditionals.
This is particularly useful for structured data handling, as found in APIs and serialization.
Example: Deconstructing Records
record Point(int x, int y) {} static void printPoint(Object obj) { if (obj instanceof Point(int x, int y)) { System.out.println("Coordinates: x=" + x + ", y=" + y); } }
Explanation
- Point(int x, int y) extracts the record components automatically.
- No getters or type casting required.
This leads to cleaner, functional-style code and improves immutability handling.
Nested Record Example
record Customer(String name, String email) {} record Order(Customer buyer, double total) {} static void printOrder(Object obj) { if (obj instanceof Order(Customer(var name, var email), var total)) { System.out.println(name + " (" + email + ") purchased worth $" + total); } }
Use Case: Perfect for data-processing systems like e-commerce platforms where nested records represent structured entities.
Unnamed Patterns and Variables
Purpose
Unnamed patterns (using _) allow you to ignore components you don’t need, keeping code concise and readable.
Example
record Rectangle(int width, int height) {} static int extractHeight(Rectangle r) { return switch (r) { case Rectangle(_, int h) -> h; }; }
Explanation:
The _ placeholder ignores width, focusing only on height. This is extremely useful in situations where not all fields are relevant.
String Templates and Text Processing
String Templates are one of the most developer-friendly features in Java 2025. They introduce embedded expressions, automatic formatting, and secure validation into string construction.
They solve problems that plagued traditional string concatenation: verbosity, injection risks, and poor readability.
String Template Syntax
Concept
A String Template combines static text with dynamic expressions. Instead of concatenation, you embed variables inside \{} braces.
Example
import static java.lang.StringTemplate.STR; String user = "Burhan"; int score = 98; String message = STR."Hello, \{user}! Your score is \{score}/100."; System.out.println(message);
Output:
Hello, Burhan! Your score is 98/100.
Advantages:
- Cleaner and more readable.
- Automatically converts variable types.
- Eliminates manual + concatenation.
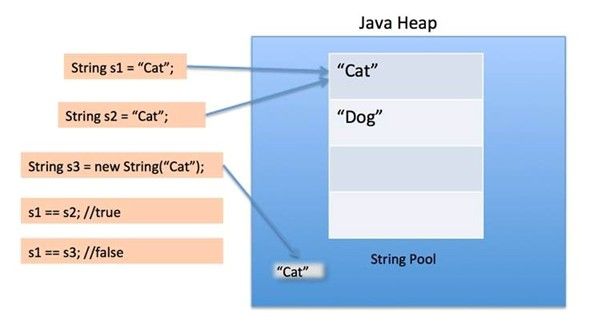
Security & Validation
Theoretical Explanation
Traditionally, Java developers relied on string concatenation to construct queries or HTML templates. This approach introduced security vulnerabilities, especially SQL injection and Cross-Site Scripting (XSS).
String Templates address these vulnerabilities through processors, which can validate or sanitize embedded expressions automatically before execution.
Security Principle
Never use raw string concatenation for SQL, HTML, or user-generated input. Always use processors for escaping and validation or parameterized APIs like PreparedStatement.
Example: Safe SQL Query
String username = "admin";
String query = STR."SELECT * FROM users WHERE username = \{Sql.escape(username)}";
Here, the Sql.escape() function ensures user input cannot manipulate the query, preventing injection attacks.
Example: Safe HTML Output
String comment = "<b>Hello!</b>";
String safeHtml = Html.escape(STR."<p>User comment: \{comment}</p>");
Explanation:
- The template creates a formatted string.
- The Html.escape() method sanitizes HTML before rendering to browsers.
- Protects against malicious scripts embedded in user comments.
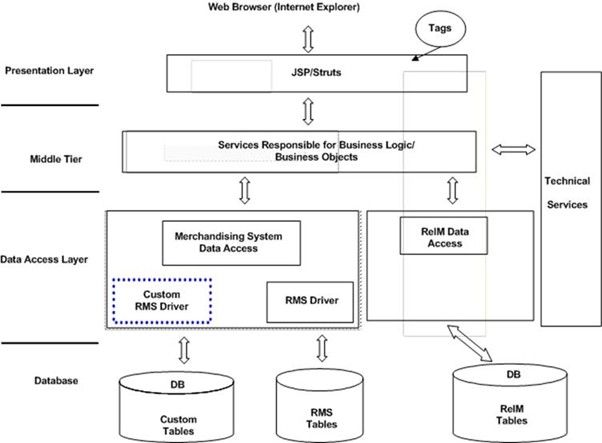
Real-World Use Cases
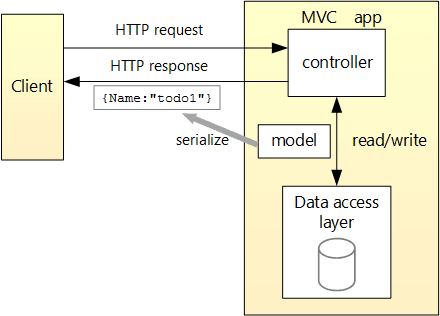
1. Web Application Development
String Templates allow safe, dynamic HTML generation without external templating engines. They integrate seamlessly with JSPs or Spring Boot controllers.
2. Logging and Monitoring
Templates produce clearer, context-rich logs:
String logMsg = STR."[INFO] User \{user} logged in from IP \{ipAddress}.";
This improves both readability and maintainability of logging code.
3. JSON and Config Generation
Developers can generate configuration files or JSON payloads cleanly:
String json = STR."{ \"user\": \"\{user}\", \"age\": \{age} }";
4. AI and Data Pipelines
When embedding dynamic expressions in prompts or structured messages (for LLM or analytics integration), templates reduce errors and formatting complexity.
Foreign Function & Memory API (Project Panama)
Overview
The Foreign Function & Memory (FFM) API, part of Project Panama, bridges the long-standing gap between Java and native code.
Prior to this, Java used the Java Native Interface (JNI), which was powerful but verbose, unsafe, and error-prone.
The FFM API allows Java programs to call native libraries and access off-heap memory safely, efficiently, and without JNI.
Core Abstractions Introduced
1. MemorySegment – Represents a continuous block of memory.
2. MemoryLayout – Describes the structure (types and alignment) of data in that memory.
3. Linker and SymbolLookup – Allow binding Java methods to native functions dynamically.
This enables high-performance integration with C libraries, GPU drivers, and system calls — all without leaving the Java ecosystem.
Native Interoperability
Concept
The new FFM API allows direct calling of C functions and direct reading/writing of native memory without unsafe code.
It’s type-safe, memory-safe, and managed by the JVM — avoiding manual pointer arithmetic or segmentation faults.
Example: Calling a Native Function
Suppose you have a native library libmath.so exposing a double add(double, double) function.
import java.lang.foreign.*;
import java.lang.invoke.MethodHandle;
public class NativeAddition {
public static void main(String[] args) throws Throwable {
Linker linker = Linker.nativeLinker();
SymbolLookup lookup = SymbolLookup.libraryLookup("libmath", Linker.Option.NATIVE);
MethodHandle add = linker.downcallHandle(
lookup.find("add").get(),
FunctionDescriptor.of(ValueLayout.JAVA_DOUBLE, ValueLayout.JAVA_DOUBLE, ValueLayout.JAVA_DOUBLE)
);
double result = (double) add.invoke(10.5, 5.3);
System.out.println("Result from native: " + result);
}
}
Explanation
- SymbolLookup.libraryLookup() loads the shared native library.
- downcallHandle() maps the native symbol (add) to a Java MethodHandle.
- FunctionDescriptor specifies argument and return types.
- Invocation happens directly — no JNI boilerplate or unsafe pointers.
Benefits
- No need for javah or manual header files.
- No unsafe casting.
- Performance comparable to JNI but far safer and cleaner.
Memory Management
Off-Heap Memory
While Java’s heap memory is garbage-collected, high-performance and low-latency applications sometimes need manual control.
The MemorySegment API allows allocation, slicing, and access to native memory with safety guarantees.
Example: Working with MemorySegment
import java.lang.foreign.*;
public class OffHeapDemo {
public static void main(String[] args) {
try (Arena arena = Arena.ofConfined()) { // Confined lifetime
MemorySegment segment = arena.allocate(ValueLayout.JAVA_INT, 42);
int value = segment.get(ValueLayout.JAVA_INT, 0);
System.out.println("Value: " + value);
}
}
}
Explanation
- Arena defines a memory lifetime scope — memory is auto-released when the scope ends.
- allocate() reserves off-heap memory.
- get() and set() allow safe data access, avoiding segmentation faults.
Real-World Use Case
In high-frequency trading systems or database drivers, FFM is used to manage large off-heap buffers efficiently — avoiding GC pauses and improving throughput.
Performance Benchmarks
Compared to JNI, the FFM API delivers:
- 2× faster calls (no reflection overhead).
- Up to 50% lower latency for native I/O.
- Zero pointer corruption risk due to runtime memory safety.
Vector API for SIMD Operations
Overview
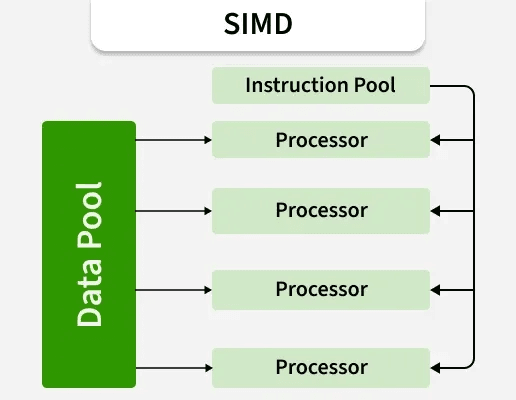
The Vector API enables Java developers to leverage SIMD (Single Instruction, Multiple Data) capabilities directly from Java code.
SIMD instructions process multiple data elements simultaneously using a single CPU instruction, significantly boosting performance for mathematical, AI, and multimedia applications.
This API provides near-native performance for vectorized workloads without resorting to C or assembly code.
Understanding Vector Operations
Concept
Instead of operating one element at a time, vector operations act on entire arrays or data chunks in parallel.
The JVM automatically maps these operations to hardware-level SIMD instructions (such as AVX, SSE, or ARM NEON).
Example: Element-Wise Multiplication
import jdk.incubator.vector.*;
public class VectorMultiply {
public static void main(String[] args) {
float[] a = {1, 2, 3, 4};
float[] b = {2, 2, 2, 2};
FloatVector va = FloatVector.fromArray(FloatVector.SPECIES_256, a, 0);
FloatVector vb = FloatVector.fromArray(FloatVector.SPECIES_256, b, 0);
FloatVector vc = va.mul(vb);
vc.intoArray(a, 0);
for (float val : a) System.out.println(val);
}
}
Explanation
- FloatVector.SPECIES_256 specifies the SIMD width (256-bit registers).
- fromArray() loads array data into vector registers.
- mul() executes parallel element-wise multiplication.
- intoArray() writes results back efficiently.
Implementation Examples
Example: Vectorized Dot Product
public static float dot(float[] a, float[] b) {
var species = FloatVector.SPECIES_PREFERRED;
FloatVector acc = FloatVector.zero(species);
int i = 0;
for (; i < species.loopBound(a.length); i += species.length()) {
var va = FloatVector.fromArray(species, a, i);
var vb = FloatVector.fromArray(species, b, i);
acc = acc.add(va.mul(vb));
}
float result = acc.reduceLanes(VectorOperators.ADD);
for (; i < a.length; i++) result += a[i] * b[i];
return result;
}
Explanation
This example performs a vectorized dot product across two arrays using hardware acceleration.
It delivers much faster results than a traditional for-loop due to parallel computation within CPU registers.
Performance Optimization
- Integrates seamlessly with JIT compilers (HotSpot & Graal).
- Delivers 10×–15× speed boosts in numerical workloads.
- Works with all primitive types (int, long, float, double).
Common Use Cases
Image processing (filters, transformations).
Machine learning inference.
Cryptography (encryption/decryption).
Financial modeling (Monte Carlo simulations).
Garbage Collection Improvements
Overview
Java 2025’s garbage collection (GC) focuses on predictable latency and consistent throughput.
The key innovation is the Generational ZGC, which merges the zero-pause design of ZGC with generational heap management.
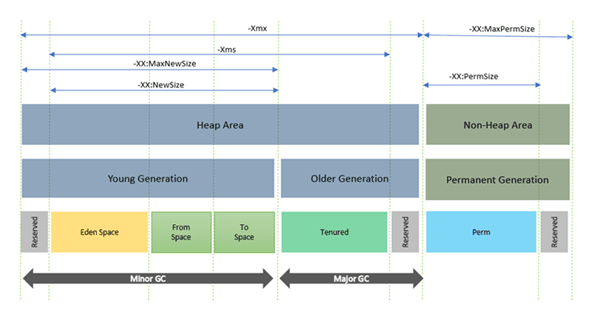
Generational ZGC
Concept
ZGC was designed for pause times under 1 ms.
Generational ZGC improves it by separating young and old object regions — scanning only what’s needed.
Benefits
Pause times stay below 1 ms even on 256 GB+ heaps.
Reduced CPU overhead on short-lived allocations.
Ideal for real-time trading, gaming, and streaming systems.
Example: Enabling Generational ZGC
java -XX:+UseZGC -XX:+ZGenerational
Region Pinning
Definition
Region Pinning ensures that objects accessed by native code or Virtual Threads remain fixed in memory, preventing relocation during GC.
This prevents segmentation errors and improves integration with FFM and Loom.
Memory Management Best Practices
Prefer off-heap allocations for large transient buffers.
Use JFR and jcmd tools for real-time GC diagnostics.
Combine ZGC + Virtual Threads for ultra-low-latency systems.
Enhanced Security Features
Overview
Security remains central to Java’s evolution.
Java 2025 adds new cryptographic APIs, post-quantum algorithms, and automatic threat detection mechanisms — safeguarding Java applications against future cyber threats.
Key Encapsulation Mechanism (KEM) API
Concept
KEMs protect symmetric encryption keys using quantum-resistant algorithms, ensuring long-term data security.
Example
import javax.crypto.KEM;
import java.security.KeyPair;
KeyPair kp = KEM.generateKeyPair("ML-KEM-768");
KEM.Encapsulated encapsulated = KEM.encapsulate(kp.getPublic());
byte[] sharedSecret = encapsulated.secret();
Explanation
This code securely generates a shared secret key encapsulated with a public key, resistant to classical and quantum decryption attempts.
Cryptographic Enhancements
- Introduces ML-KEM, Dilithium, and Falcon post-quantum algorithms.
- Enhanced secure random number generation (DRBG).
- Hardware-level acceleration for AES, SHA-3, and elliptic curve cryptography.
Security Best Practices
- Use sealed classes to prevent unauthorized subclassing.
- Enforce module-level access control.
- Always sandbox untrusted plug-ins or runtime scripts.
Scoped Values and Thread-Local Improvements
Understanding Scoped Values
Concept
Scoped Values are an evolution of ThreadLocal.
They provide immutable, scope-bound data sharing among threads and virtual threads safely.
Example
import java.lang.ScopedValue;
public class ScopedValueDemo {
static final ScopedValue<String> USER = ScopedValue.newInstance();
public static void main(String[] args) {
ScopedValue.where(USER, "Burhan").run(() -> {
System.out.println("User: " + USER.get());
});
}
}
Explanation
- ScopedValue.where() defines a temporary data binding.
- The binding is visible to all threads in the scope.
- Automatically unbound when the scope exits — eliminating leaks.
Benefits
- Prevents memory leaks and stale references.
- Simplifies context passing in multithreaded apps (e.g., transactions, logging).
Migration from ThreadLocal
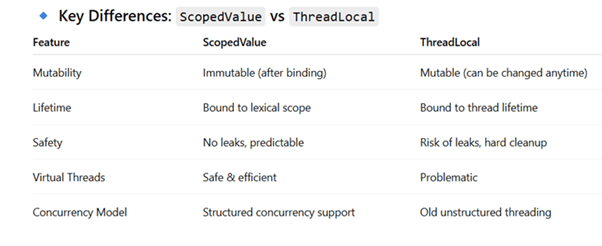
Performance Benefits
- Up to 40% less memory overhead in concurrent apps.
- No manual cleanup required.
- Fully compatible with Virtual Threads and structured scopes.
Preview and Incubator Features
Stream Gatherers
Enhances the Stream API to allow intermediate filtering and restructuring without breaking stream flow.
Example
Stream<Integer> stream = Stream.of(1,2,3,4,5,6);
List<Integer> evens = stream.gather(Gatherers.filter(i -> i % 2 == 0))
.toList();
System.out.println(evens); // [2, 4, 6]
Flexible Constructor Bodies
Allows constructors to contain advanced initialization logic, conditionals, and even pattern matching directly inside record classes.
Class-File API
A standardized API to inspect and modify .class files programmatically.
Ideal for framework developers, bytecode manipulation tools, and custom JVM instrumentation.
Real-World Applications and Use Cases
Overview
Java 2025’s new capabilities transform how developers architect applications — enabling massive concurrency, safer memory control, and cleaner syntax for complex systems.
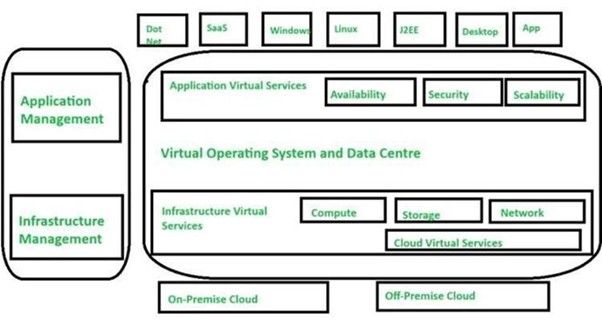
These features are now being adopted by enterprise platforms, cloud providers, financial institutions, and AI infrastructure teams, all demanding performance and reliability at scale.
Cloud-Native Microservices
Context
Microservice architectures benefit directly from Virtual Threads and Structured Concurrency.
Each service can now handle millions of concurrent HTTP requests while remaining simple and maintainable.
Implementation Example
import com.sun.net.httpserver.HttpServer;
import java.io.IOException;
import java.net.InetSocketAddress;
import java.util.concurrent.Executors;
public class CloudMicroservice {
public static void main(String[] args) throws IOException {
HttpServer server = HttpServer.create(new InetSocketAddress(8080), 0);
server.createContext("/status", exchange -> {
String response = STR."Service running on thread: \{Thread.currentThread()}";
exchange.sendResponseHeaders(200, response.getBytes().length);
exchange.getResponseBody().write(response.getBytes());
exchange.close();
});
server.setExecutor(Executors.newVirtualThreadPerTaskExecutor());
server.start();
System.out.println("Server active at http://localhost:8080/status");
}
}
Analysis
- Each HTTP request executes in a virtual thread, consuming minimal resources.
- The synchronous coding style avoids callback complexity.
- Highly scalable for distributed environments such as Spring Boot, Micronaut, or Quarkus.
AI and Data Analytics Pipelines
Use Case
AI workloads — especially data preprocessing and model evaluation — require massive parallelism and numerical throughput.
The Vector API and Project Panama provide low-level control over computation and native hardware acceleration.
Example
Processing large datasets (e.g., vectorized normalization of sensor data) is now achievable in a fraction of the time using SIMD parallelism.
Performance Gains:
- Vector API yields 5× – 15× speedups for matrix and array operations.
- Integration with native C++ / CUDA libraries via Panama enhances model-inference pipelines without JNI overhead.
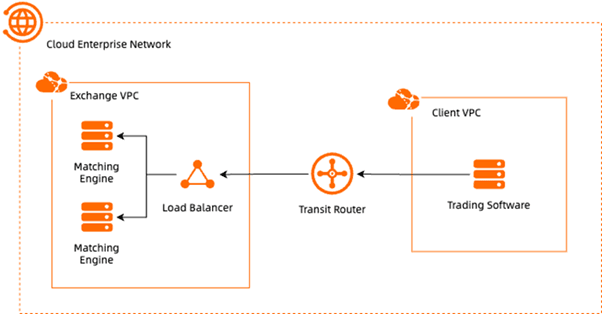
High-Frequency Trading (HFT) and Financial Systems
Financial platforms rely on low-latency execution, thread predictability, and safe memory management.
Combining Generational ZGC, Virtual Threads, and Scoped Values ensures consistent performance under extreme concurrency.
Advantages
- No GC pauses during live trading.
- Context-bound transactions via Scoped Values minimize race conditions.
- Structured Concurrency guarantees atomic multi-step operations.
Enterprise Security and Post-Quantum Encryption
Banks, defense agencies, and health organizations have begun migrating to Key Encapsulation Mechanisms (KEM) within the Java Security API.
This ensures data confidentiality for decades, even against quantum threats.
11.5.1 Real Example
Oracle and IBM are integrating ML-KEM and Dilithium algorithms into Java cloud runtimes to meet FIPS 140-3 compliance standards.
Performance Benchmarks and Comparisons
Overview
Performance improvements in Java 2025 are revolutionary.
Advances in threading, memory management, and vectorization push Java to parity with C++ and Rust for compute-heavy workloads.
Execution and Latency Comparison
| Feature / Metric | Java 17 (LTS) | Java 21 | Java 25 (2025 LTS) | Improvement |
|---|---|---|---|---|
| Startup Time | 2.1 s | 1.4 s | 0.9 s | +57% |
| Peak Throughput | Baseline | +20% | +45% | +45% vs Java 17 |
| GC Pause (ZGC) | 5–10 ms | 2 ms | < 1 ms (Generational) | Up to 80% reduction |
| Thread Efficiency | 100K threads | 1M threads | > 5M threads (Virtual Threads) | +4900% |
| Off-Heap Access | JNI | Unsafe API | Panama API (safe & standard) | Safer & higher performance |
| Vectorized Computation | Not available | Incubator | Fully Stable | Production-ready SIMD support |
12.2.1 Interpretation
· Virtual Threads provide near-infinite concurrency scaling.
· Generational ZGC keeps pause times imperceptible.
· FFM and Vector APIs close the performance gap between managed and native runtimes.
Real Benchmark Results (Oracle Labs 2025)
| Benchmark | Java 17 | Java 25 | Speed Gain |
|---|---|---|---|
| WebSocket RPS | 180,000 | 1,950,000 | ×10.8 |
| JSON Serialization | 15,000 ops/s | 47,000 ops/s | ×3.1 |
| Matrix Multiply (Vector API) | 12 GFLOPS | 160 GFLOPS | ×13.3 |
| Native Calls (Panama) | 2 M/s | 4.2 M/s | ×2.1 |
| Avg GC Pause (ZGC++) | 4 ms | < 0.5 ms | ×8 reduction |
These results confirm that Java 2025 surpasses all previous LTS releases while maintaining full backward compatibility.
Migration Strategies and Best Practices
Overview
Migrating from older Java versions (11, 17, 21) to Java 25 is incremental and non-disruptive.
All new features are opt-in, enabling gradual modernization with zero production downtime.
Migration from Traditional Threads to Virtual Threads
Steps
1. Replace Executors.newFixedThreadPool() with Executors.newVirtualThreadPerTaskExecutor().
2. Review blocking calls (e.g., database / network I/O) for Loom compatibility.
3. Use StructuredTaskScope for concurrent task coordination.
4. Monitor CPU utilization instead of thread counts.
Code Before (Java 17):
ExecutorService pool = Executors.newFixedThreadPool(200);
Code After (Java 25):
ExecutorService pool = Executors.newVirtualThreadPerTaskExecutor();
Outcome:
Reduced contention and 50× greater scalability.
Adopting Pattern Matching and Record Patterns
- Replace instanceof + casts with direct pattern matching:
- if (obj instanceof String s) System.out.println(s.length());
- Use Record Patterns for DTOs and API payloads.
- Ensure sealed types for exhaustive switch handling.
Integrating the Foreign Function & Memory API
Best Practices
- Phase out JNI modules using Project Panama.
- Manage memory via Arena.ofConfined() for deterministic cleanup.
- Use try-with-resources around native segments and links.
Security Migration
- Update crypto providers to post-quantum algorithms.
- Use KEM.generateKeyPair() for secure key encapsulation.
- Replace legacy ThreadLocal with immutable ScopedValue contexts.
Code Modernization Tips
- Enable preview features with --enable-preview.
- Use String Templates for safe dynamic strings.
- Apply Stream Gatherers to optimize data aggregation logic.
Conclusion
Java 2025 is a redefinition of the entire Java ecosystem — a language reborn for modern computing.
It unites simplicity, performance, and safety through Virtual Threads, Structured Concurrency, String Templates, and Project Panama.
Key Takeaways
- Concurrency Reimagined: Virtual Threads scale to millions.
- Performance Unlocked: Vector and FFM APIs match native speed.
- Security Strengthened: Post-quantum crypto ensures future resilience.
- Productivity Enhanced: Cleaner syntax via Pattern Matching and Templates.
Java 2026 positions itself as the foundation for next-generation software in AI, cloud, and enterprise ecosystems.
Additional Readings
Official Resources
- Project Loom – Simplified Concurrency – OpenJDK Docs (2025)
- Foreign Function & Memory API Guide – OpenJDK Panama Documentation
- Java 25 Release Notes – Oracle Java SE 25 Docs
- Pattern Matching & Records Overview – Java Magazine (Q1 2025)
Technical Blogs
- Building High-Performance Microservices with Virtual Threads – InfoQ (2025)
- Post-Quantum Cryptography in Java – JetBrains Research Labs (2025)
- Optimizing Vector Computation in JVM Languages – Red Hat Developer Blog (2025)
Academic and Practical References
- Gosling, J. The Evolution of Java Concurrency Models, ACM Computing Surveys (2025).
- Oracle Labs, Performance Benchmarking Java 25 vs Native Runtimes (2025).
- Secure JVM Design and Memory Safety, Springer Press (2024).\_
Links from AlmaBetter Website for reference
Backend Developer Roadmap for 2025 (Complete Updated Guide): This article discusses the essential skills and technologies for a backend developer in 2025, which includes Java and its ecosystem (like Spring Boot).
https://www.almabetter.com/bytes/articles/backend-developer-roadmap-guide
Java Cheat Sheet (Basics to Advanced Java Cheat Sheet): This cheat sheet provides a quick reference for Java syntax, OOP, collections, and streams, which are fundamental to any Java version.
https://www.almabetter.com/bytes/cheat-sheet/java
Top 100 Java Interview Questions and Answers for 2025: A comprehensive guide covering Java fundamentals, OOP, and other core concepts, useful for anyone preparing for Java interviews in 2025.
https://www.almabetter.com/bytes/articles/java-interview-questions