Your Success, Our Mission!
6000+ Careers Transformed.
Explanation
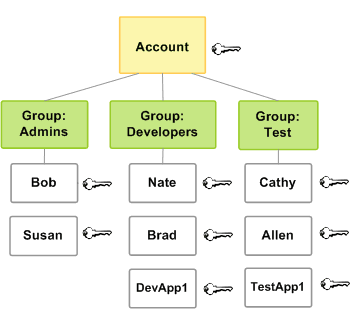
AWS Identity and Access Management (IAM) is the core service used to control access to AWS resources. It enables authentication and authorization through users, groups, roles, and policies. IAM policies define permissions using a JSON-based language that specifies allowed or denied actions on resources. Roles allow secure access without long-term credentials and are commonly used by AWS services and applications. IAM supports multi-factor authentication, fine-grained access control, and integration with external identity providers, forming the foundation of AWS security.
Table
| IAM Component | Purpose |
|---|---|
| User | Individual identity |
| Group | Collection of users |
| Role | Temporary permissions |
| Policy | Permission definition |
| MFA | Additional authentication |
Example
A development team creates IAM users for each engineer and assigns them to groups with predefined permissions. Applications running on EC2 assume IAM roles instead of storing access keys. Multi-factor authentication is enabled for sensitive operations. Permissions are reviewed regularly to enforce least privilege. This approach minimizes security risks and simplifies access management.
Use Cases
• Secure access control
• Least-privilege permission management
• Application authentication
• Cross-account access
Top Tutorials

CNN in Deep Learning 2026
A beginner-friendly guide to CNNs: understand deep learning essentials, create Python-based models, and explore advanced applications.

Breaking The Limits: Scaling Databases with MySQL Partitioning
Learn MySQL partitioning with examples. Improve query performance, scalability, and data management using RANGE, LIST, HASH, KEY, and composite techniques.

ML in Action: Hands-On Guide to Deploying and Serving Models
Learn model deployment and serving—from concepts to real-world architectures, tools, APIs, containers, and cloud workflows for production-ready ML.
All Courses (6)
Master's Degree (2)
Fellowship (2)
Certifications (2)